14 iPhone apps covertly talking to suspect Golduck malware server
Security researchers say they’ve found more than a dozen iPhone apps covertly communicating with a server associated with Golduck, a historically Android-focused malware that infects popular classic game apps.
The malware has been known about for over a year, after it was first discovered by Appthority infecting classic and retro games on Google Play, by embedding backdoor code that allowed malicious payloads to be silently pushed to the device. At the time, more than 10 million users were affected by the malware, allowing hackers to run malicious commands at the highest privileges, like sending premium SMS messages from a victim’s phone to make money.
Now, the researchers say iPhone apps linked to the malware could also present a risk.
Wandera, an enterprise security firm, said it found 14 apps — all retro-style games — that were communicating with the same command and control server used by the Golduck malware.
“The [Golduck] domain was on a watchlist we established due to its use in distributing a specific strain of Android malware in the past,” said Michael Covington, Wandera’s vice-president of product. “When we started seeing communication between iOS devices and the known malware domain, we investigated further.”
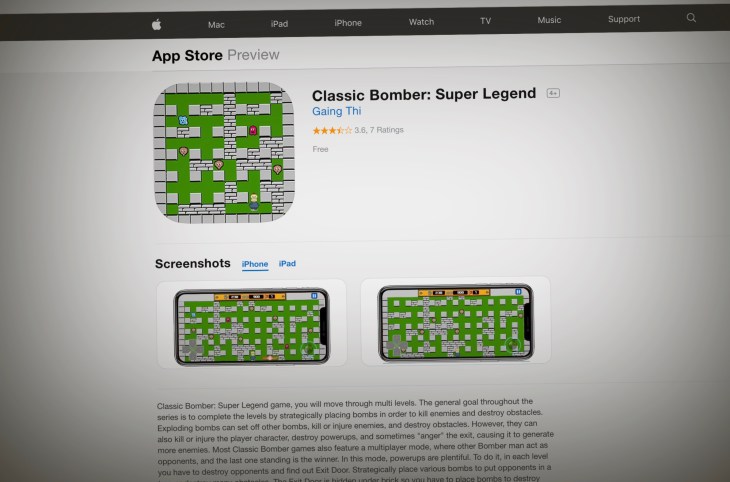
The apps include: Commando Metal: Classic Contra, Super Pentron Adventure: Super Hard, Classic Tank vs Super Bomber, Super Adventure of Maritron, Roy Adventure Troll Game, Trap Dungeons: Super Adventure, Bounce Classic Legend, Block Game, Classic Bomber: Super Legend, Brain It On: Stickman Physics, Bomber Game: Classic Bomberman, Classic Brick – Retro Block, The Climber Brick, and Chicken Shoot Galaxy Invaders.
According to the researchers, what they saw so far seems relatively benign — the command and control server simply pushes a list of icons in a pocket of ad space in the upper-right corner of the app. When the user opens the game, the server tells the app which icons and links it should serve to the user. They did, however, see the apps sending IP address data — and, in some cases, location data — back to the Golduck command and control server. TechCrunch verified their claims, running the apps on a clean iPhone through a proxy, allowing us to see where the data goes. Based on what we saw, the app tells the malicious Golduck server what app, version, device type, and the IP address of the device — including how many ads were displayed on the phone.
Source



